We have already covered SSL certificates preparation and conversion in the previous topic. For completeness sake, I’d like to cover another important aspect in DevOps, which is SSH keys configuration. The case where you may need an SSH key are:
- Accessing a Linux-based Virtual Machine (VM)
- Accessing Git repository
- Build/release pipeline
- Deployment automation tools like Chef/Ansible/Puppet etc.
The most widely spread case is a Linux VM instantiation. The more secure scenario would be providing an SSH key instead of just a password to login. Having cmder (console emulator) the operation is straightforward as ssh-keygen is bundled with some other useful utils out-of-the-box. If you don’t want to use that once, Git for Windows comes with the Git Bash client that has the same capability:
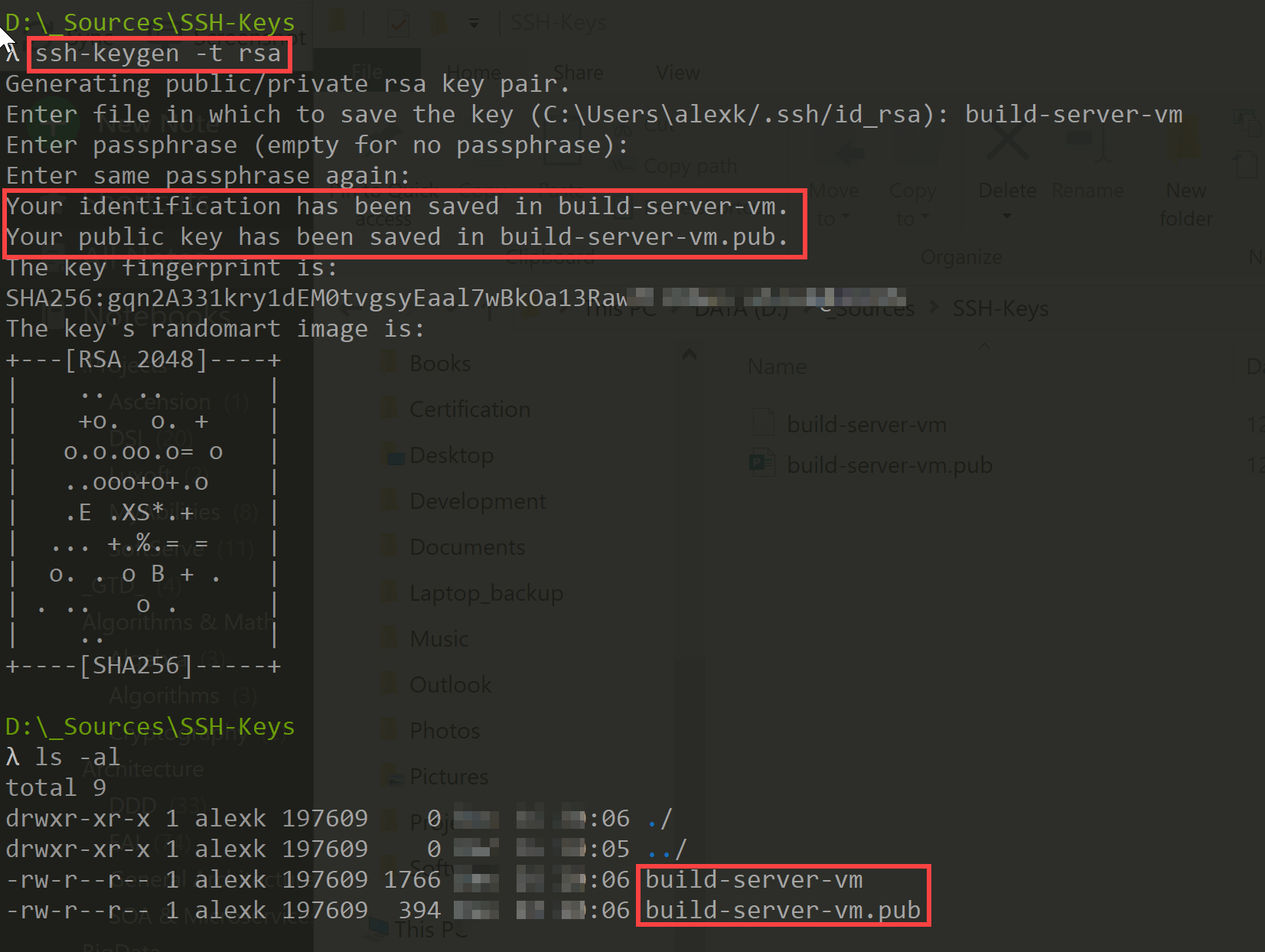
The command on the screenshot ‘ssh-keygen -t rsa’ generates a public/private key pair at the target directory. It can be parameterized so you’re creating a key with 2048 or 4096-bit length: ‘ssh-keygen -t rsa -b 4096’.
In the example above, two files were created:
- build-server-vm- this is the private key you use connecting to the VM
- build-server-vm.pub - this is the public key you will use when creating the VM
Let’s see the content:
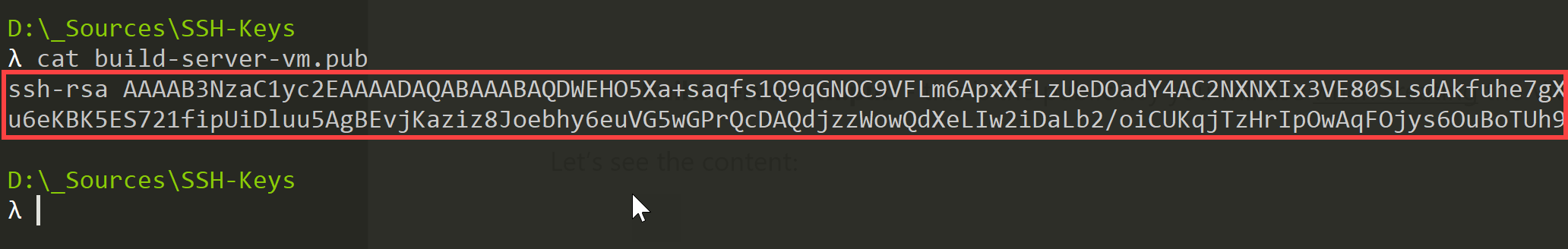
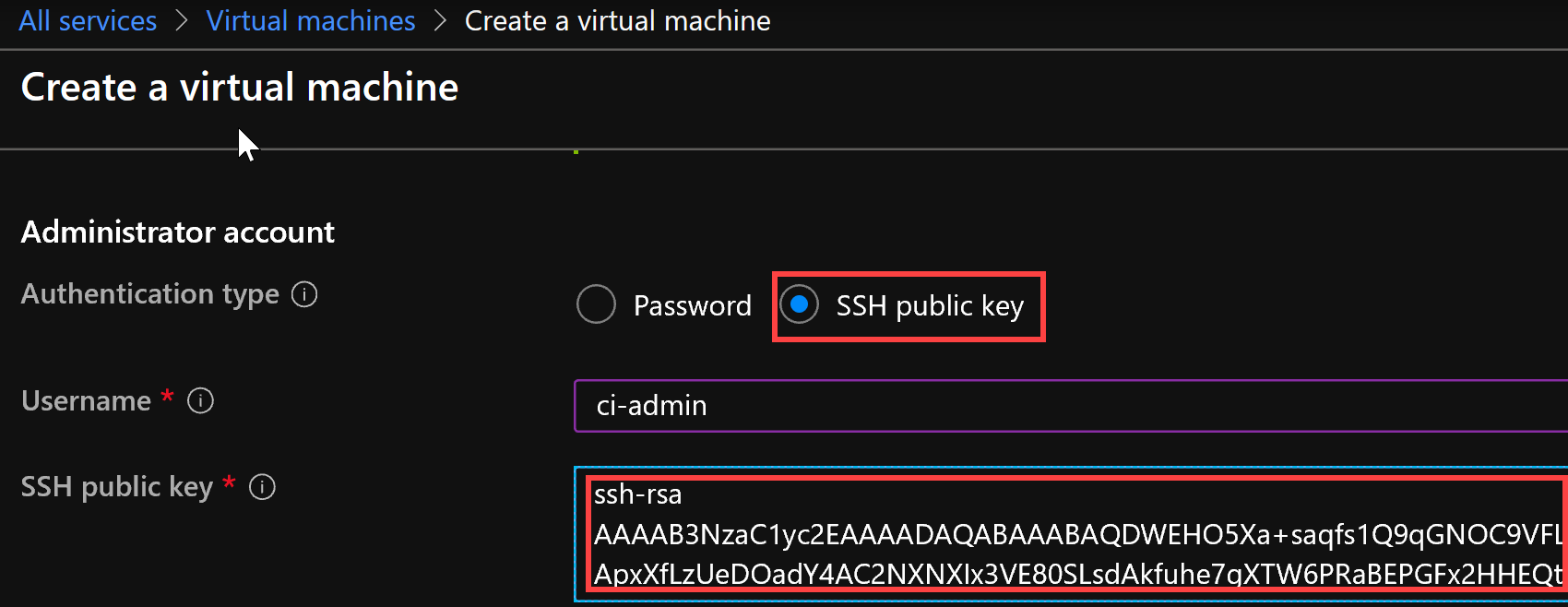
Copy the content of this file using whatever tool you’ve got available (command line or notepad) and paste it in the SSH key field when creating a VM in Azure (for instance):
Once VM is provisioned, you can access it via the same console:
ssh -i build-server-vm [email protected]
If you access the same VM on a regular basis, you can keep track of your keys using PuTTY or any other relevant SSH client.
I hope this topic demonstrated how easy it is to get with SSH keys to safely connect to a target Linux VMs. Accessing VMs in the cloud assumes a wider scope, such us key managements and using so-called Jump-servers/Jump boxes/Bastion server (all are synonyms) to access target VM in a more secure manner, which I will be covering in the upcoming topics.